I recently wrapped up a practical exercise in password recovery that reminded me of a vital rule in cybersecurity: Context is everything.
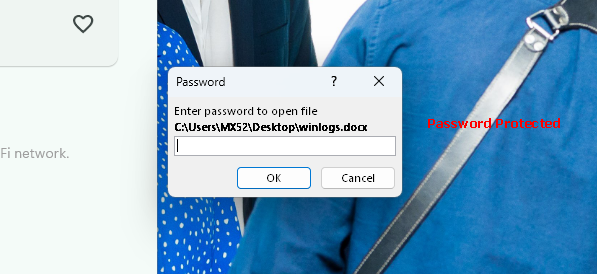
I was tasked with accessing an encrypted Microsoft Word document. Rather than relying on guesswork, I performed a structured offline analysis to recover the credential. Here’s a look at the workflow:
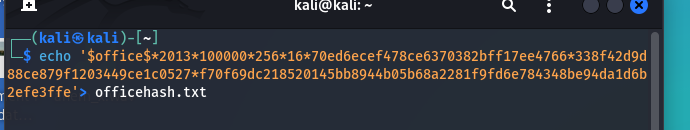
🔹 The Extraction: Using office2john, I pulled the structured hash from the file. The string $office$*2013*100000*256… told me exactly what I was dealing with: Microsoft Office 2013 encryption.
🔹 The Technical Hurdle: This wasn’t just a simple SHA-256 hash. It involved 100,000 iterations (key stretching) and AES-based verification. In the world of recovery, identifying these parameters is the difference between a successful result and hours of wasted compute time.
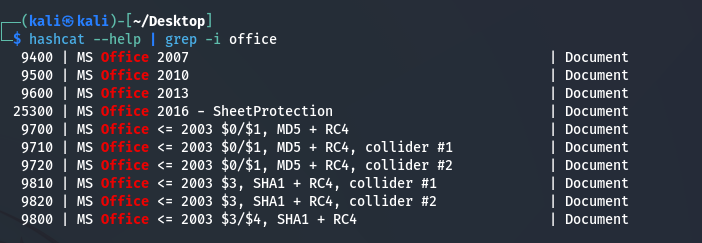
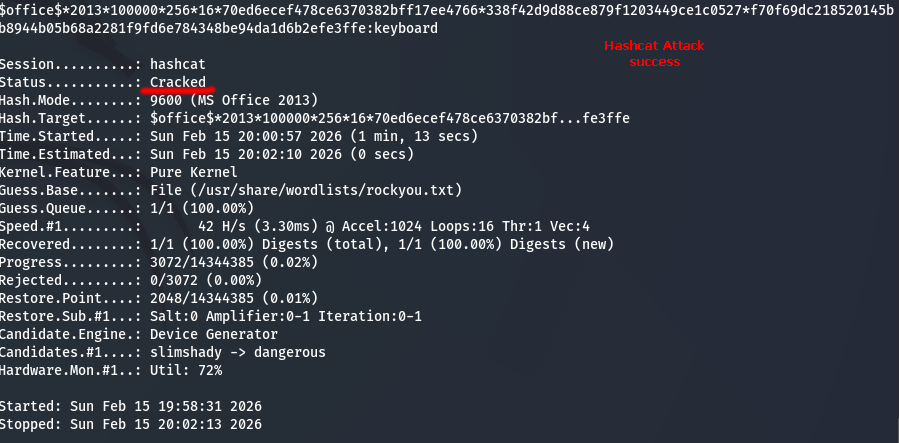
🔹 The Solution: I deployed Hashcat using Mode 9600 (specifically for Office 2013). By preserving the full $office$ structure and using a targeted wordlist, I successfully recovered the password and restored access to the data.
My Key Takeaways:
✅ Format Matters: Technical details like preserving the metadata prefix are critical for tool compatibility.
✅ Tool Proficiency: Knowing how to map a hash type to the correct attack mode (like Hashcat 9600) is a must-have skill.
✅ Patience vs. Precision: High iteration counts make attacks slow by design. Precision in your setup saves time.
This exercise was a great reminder that in cybersecurity(digital forensics), attention to detail is the ultimate shortcut.