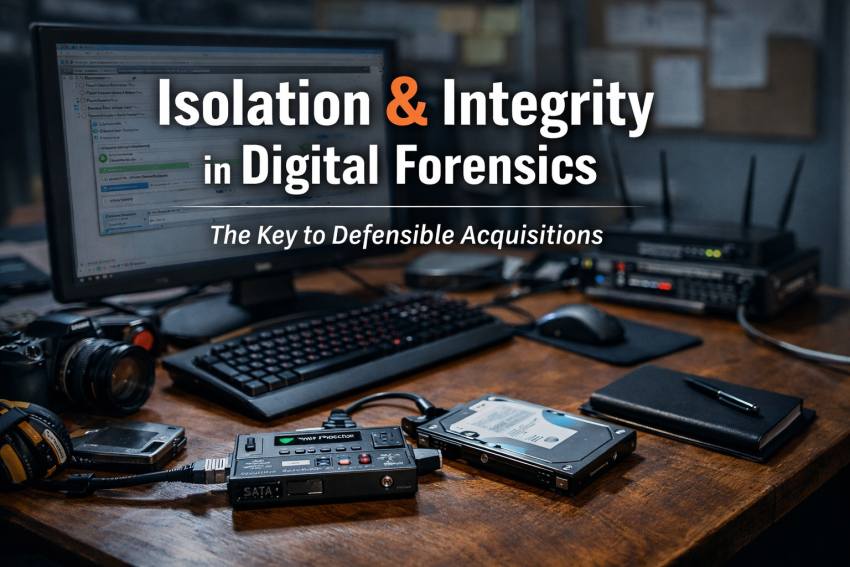
As I continue learning about disk imaging, I’ve seen the instruction: isolate the forensic workstation from networks.At first, I thought that meant disconnecting everything involved. The suspect machine. The workstation. Pull every cable. Air-gap the world.But here’s what I’ve learned.
Cracking the Code: A Deep Dive into Multi-Layer Steganography
I just wrapped up a fascinating CTF (Capture The Flag) challenge by HIVE Consult that perfectly illustrates why you should never take a file at its face value. What looked like a standard JPEG was actually a Russian Nesting Doll of hidden data.
Cracking the Code: A Lesson in Cryptographic Analysis
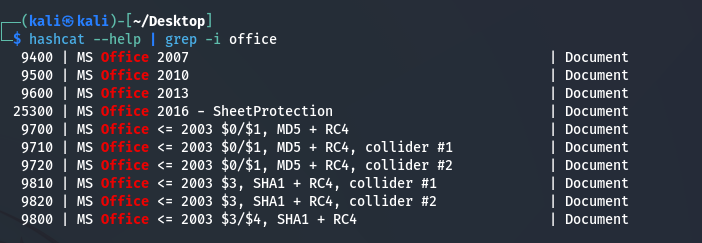
I recently wrapped up a practical exercise in password recovery that reminded me of a vital rule in cybersecurity: Context is everything.I was tasked with accessing an encrypted Microsoft Word document. Rather than relying on guesswork, I performed a structured offline analysis to recover the credential. Here’s a look at the workflow:
Deep Dive into Browser Forensics
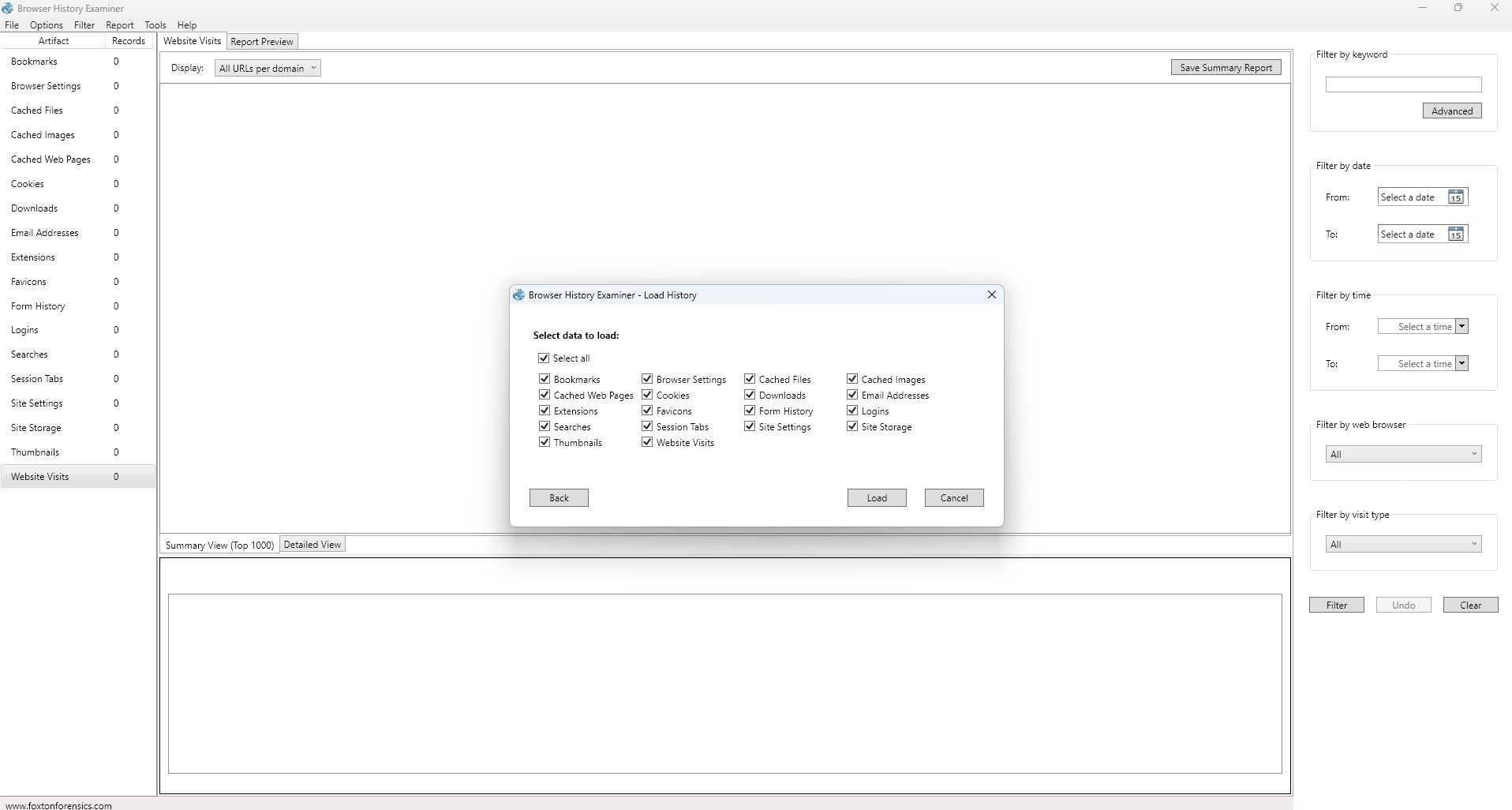
A deeper dive into Browser History Examiner during a browser forensics module with HIVE Consult surfaced an important security insight I hadn’t fully appreciated before.Browser History Examiner can reveal browser artifacts, including visited URLs, timestamps, frequency of access, browser type, and, in some cases, evidence of usernames used through form data, cached content, or autofill…
Myth about deleted history
“I cleared my history.” The five most dangerous words for a suspect, but the most interesting for an investigator.Most people think a cache wipe is a clean slate. My latest look into browser forensics proved otherwise. Working with Browser History Examiner reminded me that clearing history and caches doesn’t mean activity disappears. It usually just…
Learning Browser Forensics
Today I started Module 2 of Digital Forensics with HIVE Consult, focusing on browser forensics. As the lesson went deeper, many of the questions naturally shifted toward networking concepts.Having recently refreshed my networking fundamentals, I was able to contribute to the discussion and help clarify a few things for my peers. I also shared the…
Microsoft Certified Security Operations Analyst Associate
Yesterday, I started studying for the Microsoft Certified: Security Operations Analyst Associate on Microsoft Learn.This isn’t just about earning another certification. It’s a deliberate move to reduce mental fatigue as I transition from core fundamentals into Digital Forensics, while building a strong understanding of how modern security operations actually work.
Milestone (Certification)
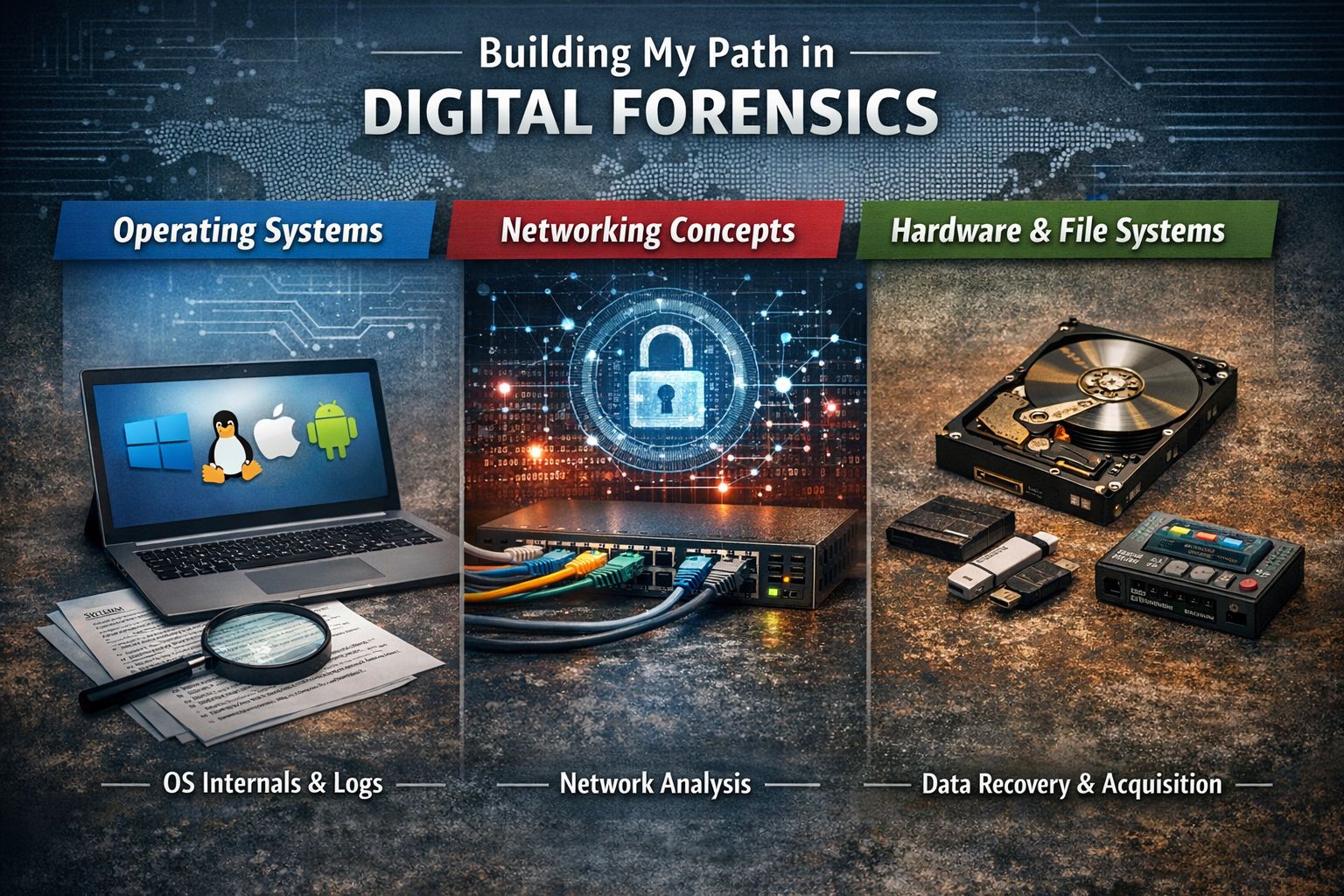
I’ve just completed the Operating Systems fundamentals on Cisco Networking Academy. This is 1 out of 3 paths I’ve mapped out for my return.
Making a comeback
Returning to tech through Digital Forensics is the goal, but goals need a clear path. After digging into what actually matters at the foundation level, this is the route I’ve chosen: • Operating Systems• Networking Concepts• Hardware and File Systems
Where have I been
I stepped away from the tech industry for a couple of years to experience life on the other side of the wall. I knew I’d regret it if I never gave myself the space to explore, to feel fulfilled, and to really understand what that other side held. Some people said I could do both…